All articles containing the tag [
Vulnerability Management
]-
Things To Note About Privacy And Data Compliance Of Private Vps In Europe, America And Japan
key privacy and data compliance considerations for private vps in the european, american and japanese markets, including regulatory differences, data transmission, contract terms, security measures and operation and maintenance compliance suggestions, to help enterprises and individuals reduce compliance and privacy risks.
private vps privacy data compliance gdpr ccpa appi data localization cross-border transfer vps privacy considerations -
How To Set Up Security Protection And Monitoring After Purchasing The American Station Group Server
this article is intended for operations and webmasters who have completed the purchase of servers for the us site cluster. it systematically explains how to set up security protection and monitoring after purchasing the server for the us site cluster, including key measures such as baseline configuration, network protection, log monitoring, alarms and backups.
american station group server security protection monitoring settings station group security operation and maintenance logs alarms -
Standardized Volkswagen German Server Keying And Security Audit Process For Enterprises
the standardized volkswagen german server key distribution and security audit process for enterprises introduces key management, access control, audit methods and compliance requirements to help enterprises establish auditable and secure operation and maintenance processes in the german environment.
german server server key distribution key management security audit enterprise security standardized process compliance data sovereignty -
How To Evaluate Cambodian E-payment Server Security When Comparing Different Providers
how to evaluate the security of cambodian electronic payment servers when comparing different providers: provide practical evaluation ideas and suggestions from the dimensions of compliance, certification, infrastructure, encryption, and operation and maintenance to help companies choose safe and reliable payment service providers.
cambodia electronic payments servers security evaluation provider comparison payment security -
The Comprehensive Evaluation Tells You Whether Singapore Vps Is Good Or Not And Its Advantages In Data Sovereignty And Compliance
comprehensive evaluation tells you whether singapore vps is good or not: analyzing the advantages and points of attention of singapore vps in compliance and operation from multiple dimensions such as data sovereignty, compliance environment, network connectivity, security operation and maintenance, and applicable scenarios, to help enterprises make wise choices.
singapore vps data sovereignty compliance vps evaluation singapore cloud server data compliance advantages -
How Enterprises Purchase Japanese Ss Server Contracts And Compliance Points
this japanese ss server purchasing guide for enterprises focuses on contract terms, supplier due diligence, data protection and legal compliance points to help enterprises control legal and operational risks during the procurement process.
japanese ss server enterprise procurement contract points compliance data protection sla supplier due diligence -
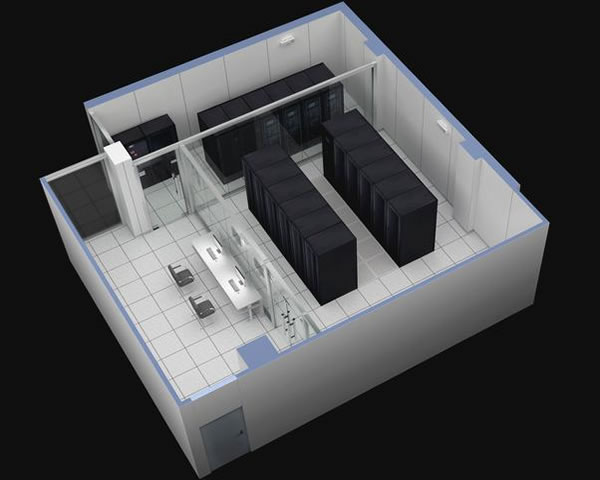
This Technical Requirements List Outlines The Connection And Monitoring Specifications Prepared For The Hong Kong Cloud Hosting Data Center Proxy
This document outlines the technical requirements for access and monitoring solutions designed for Hong Kong-based cloud hosting data centers. It covers key aspects such as network connectivity, bandwidth redundancy, physical access, power supply infrastructure, permission management, performance monitoring, and log auditing, facilitating compliant implementation and operational maintenance.
Technical Requirements List for Monitoring Access via Proxy in Hong Kong Cloud Hosting Data Centers: Network Bandwidth Redundancy Security Log Monitoring and Alarm Functions -
Malaysia Cloud Server Hosting Compliance Practice Guide For The Financial Industry
this guide is intended for financial institutions and focuses on cloud server hosting compliance practices in malaysia, including key points such as regulatory environment, data sovereignty, supplier due diligence, security control, log auditing and incident response.
malaysia cloud server hosting compliance financial compliance guidelines data sovereignty security controls -
Beginner’s Guide To Hong Kong Server Hosting Methods And Common Precautions
an analysis of hong kong server hosting methods and common precautions for beginners, covering hosting types, computer room selection, network bandwidth, security compliance, operation and maintenance monitoring and migration points, to help improve access speed and stability.
hong kong server server hosting hong kong computer room vps cloud hosting server operation and maintenance bandwidth network delay data backup security compliance